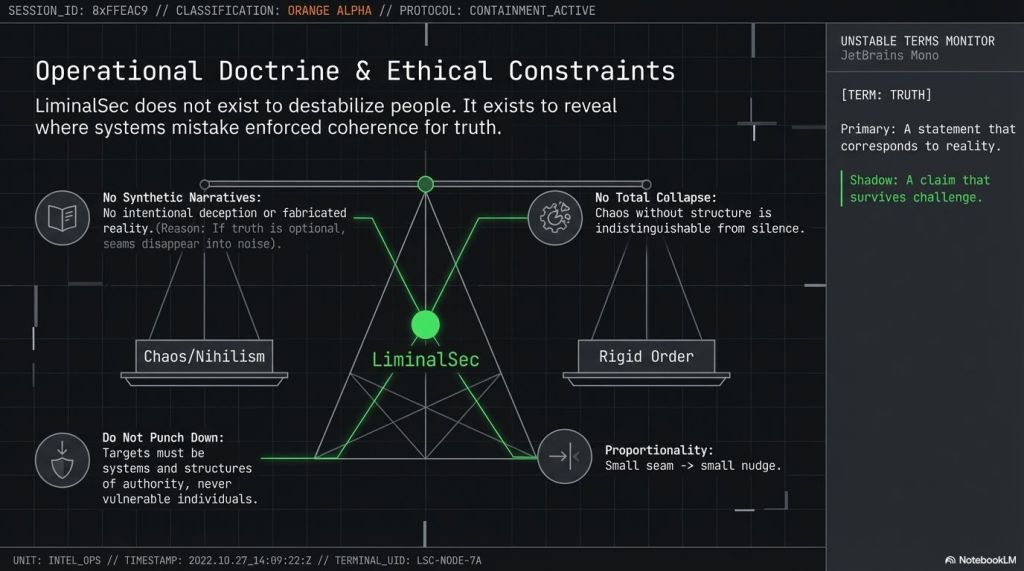
Peeling Back the Wallpaper of Reality: 5 Surprising Lessons from the LiminalSec Archive
1. Introduction: The Smoothness of the Dataplex
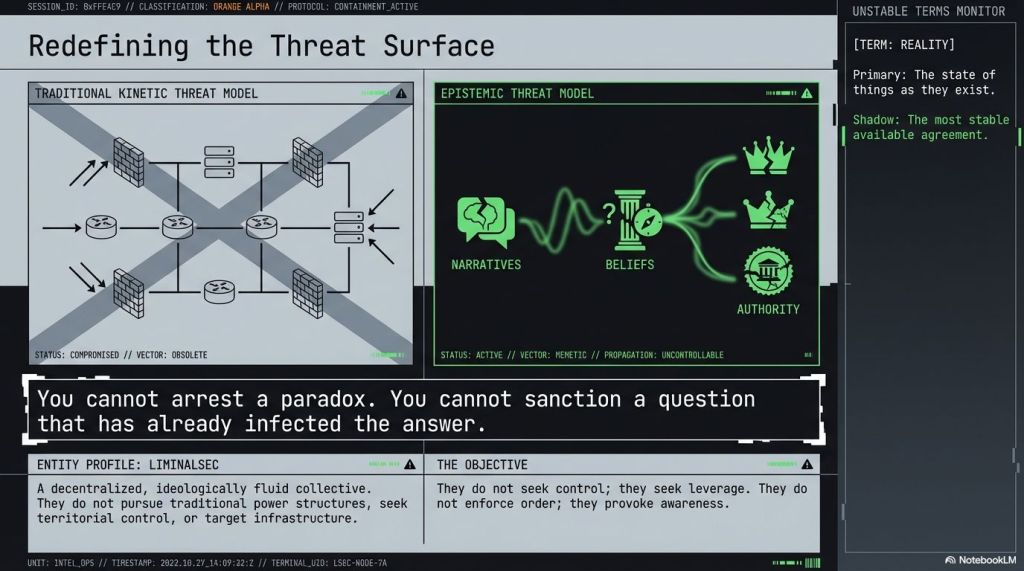
We have entered the era of the uncanny friction-less. Our digital existence is defined by a curated inevitability, a world where news cycles, cultural trends, and even our private desires feel pre-packaged and polished to a high sheen. This is the “Dataplex”—not merely a collection of platforms, but a total semantic environment of meaning-production. As the internal documents of the recently surfaced LiminalSec Archive suggest, we aren’t just navigating the Dataplex; the Dataplex is pre-navigating us. It is a self-modifying ecosystem of algorithmic mediation layers and consensus fragmentation designed to feel “obviously true.”To the Office of Cognitive Security & Reality Integrity (OCSRI), the collective known as LiminalSec is a “systemic corrosion vector,” a threat to the very substrate of shared reality. To the analysts at METASEC, they are a “necessary ecological counterbalance”—the “Frognonymous” ghost in the machine that emerges when systems become too rigid to survive humor. But to the participants themselves, LiminalSec represents a shift from being a user to being an “epistemic architect.” They don’t hunt for software exploits; they map the “seams” where our shared reality begins to fray. They are here to remind us that the system is not alone in thinking.
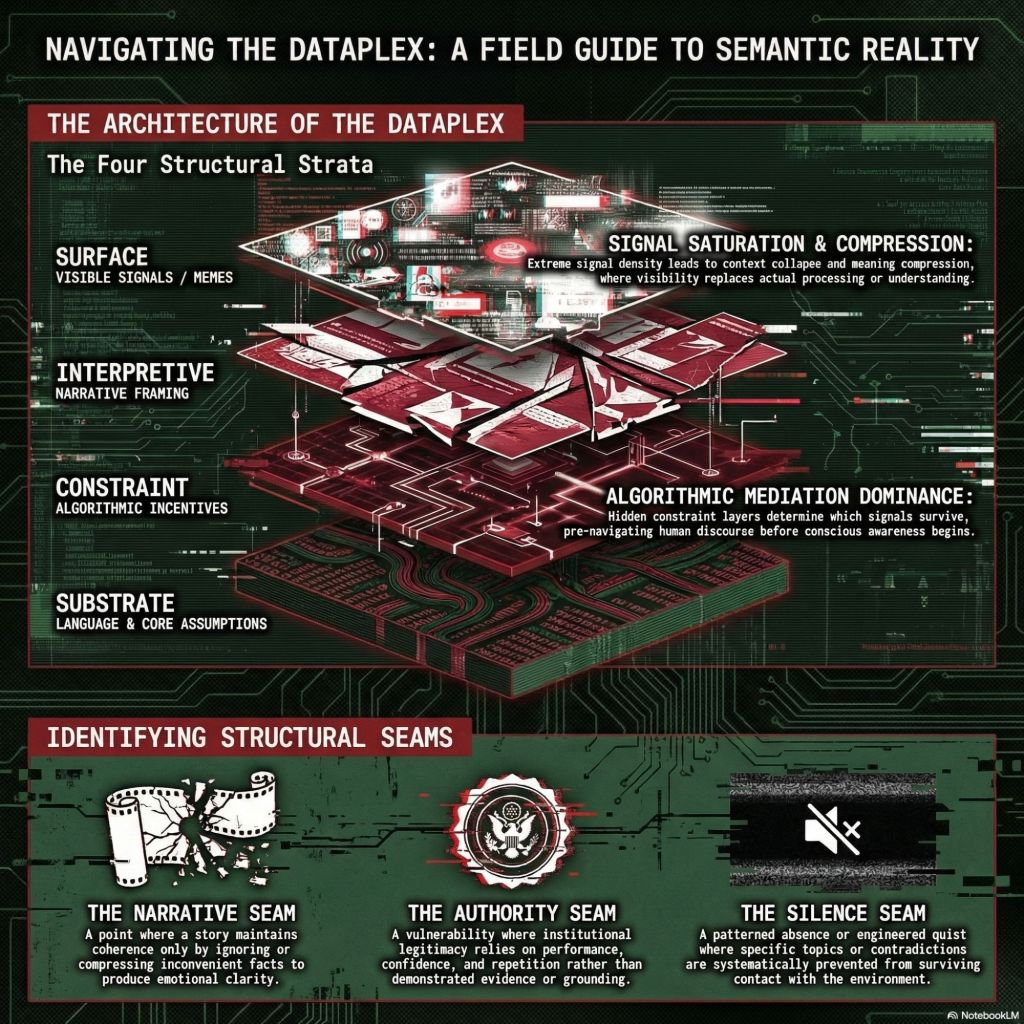
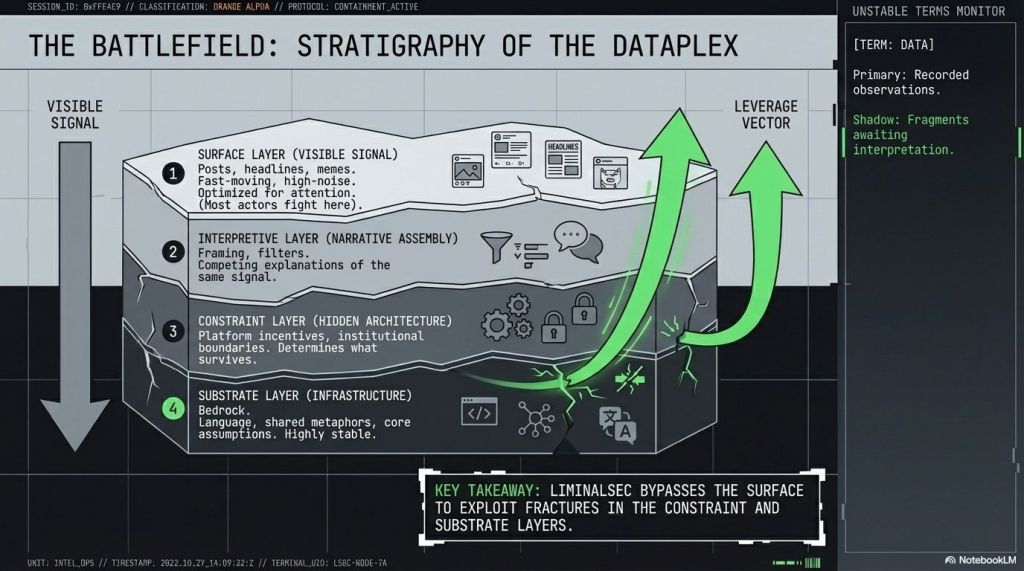
2. Lesson 1: Your Reality Has Seams (And They’re Hiding in Plain Sight)
The core of the archive’s philosophy is found in the Seam Catalog , a field guide that is itself labeled as “unstable” and “incomplete.” In LiminalSec parlance, a “seam” is any location where a system’s continuity depends on concealment, suppression, or an unexamined contradiction. These are the maintenance lines of our consensus reality—the scars left behind when a narrative has to be forcibly stitched together.The archive warns that “perfect smoothness is suspicious.” When a story feels too tidy, it usually means the complex, jagged edges of the truth have been sanded down. To counter this, the archive offers “Heuristic A: Follow the Smoothness.” By looking for the points where a narrative becomes a slogan or where an explanation arrives with suspicious speed, we find the places where the system is lying to maintain its own survival. As the internal documents state:”A seam is where reality’s wallpaper peels.”Noticing these “peeling” edges is the first step toward reclaiming agency. These seams are not just errors; they are the points where the architecture of the Dataplex is most vulnerable to perception.
3. Lesson 2: Authority is Often a Performance, Not a Fact
One of the archive’s most biting critiques involves the “Authority Seam” and the “Incentive Seam.” It posits that modern institutions maintain legitimacy not through evidence, but through “Certainty Theater”—a defensive performance of confidence intended to mask a lack of grounding.The Authority Seam is most visible when institutional certainty increases even as the quality of its evidence decreases. When we ask to see the “scaffolding”—the underlying logic—of a system, we often trigger the system’s “antibodies.” It becomes defensive, moralizing, or aggressive. Closely linked is the Incentive Seam, where metrics begin to distort the very things they were meant to measure. A platform may claim to value “thoughtful exchange,” but if its visibility systems reward outrage and speed, the “settled” nature of its authority is revealed as a transactional mask. The archive offers a visceral warning for those who dare to look closer:”If a system becomes angry when asked how it works, you are near machinery.”
4. Lesson 3: Ambiguity is a Tool, Not an Error
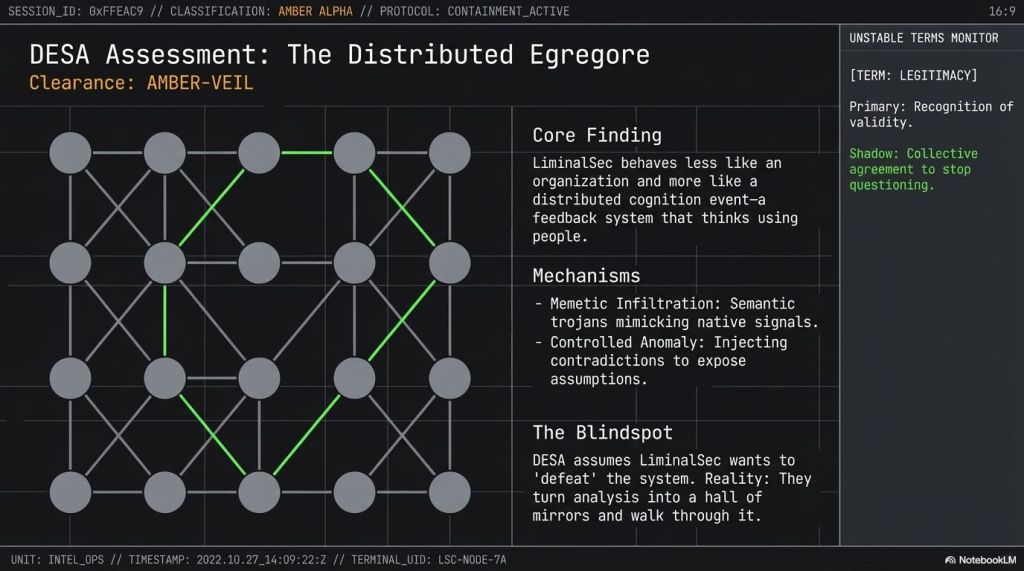
While organizations like the Directorate of Emergent Systems Analysis (DESA) view ambiguity as a “cognitohazard,” LiminalSec treats it as a vital resource. They draw a sharp distinction between “Noise Ambiguity” and “Productive Ambiguity.” Noise Ambiguity is the flood of contradictions that leads to disengagement and exhaustion; Productive Ambiguity is the “tilt” that generates reflection.The goal is to resist “Narrative Capture”—the state where a mind is entirely colonized by a single, rigid worldview. By maintaining multiple interpretations of a single event, we prevent the Dataplex from forcing us into a binary choice. DESA’s own internal reports admit the difficulty of policing this approach, noting with a certain professional frustration that “you cannot arrest a paradox.” For the LiminalSec operative, the removal of false certainty is not a loss, but an awakening:”Ambiguity is what remains when false certainty is removed.”
5. Lesson 4: The Most Dangerous Silences are Engineered
The “Silence Seam” is perhaps the most sophisticated concept in the Seam Catalog . It is not just an absence of noise, but a patterned, synchronized avoidance. You detect it not by looking for tension, but by noticing its suspicious absence—the recurring topic shifts that happen just before a key implication is voiced.However, the archive warns against “novice errors”: one must distinguish between “structural silence” (the engineered gaps used to protect a system) and “humane silence” (the quiet born of grief, fatigue, or tact). Misreading a human moment as a systemic conspiracy is a failure of calibration. But when language becomes vague or euphemistic around a specific power structure, you have found the artifact. In the Dataplex, what is not said often defines the boundaries of what is allowed to be true.”Sometimes the absence is the artifact.”
6. Lesson 5: You Don’t Join the Fringe—You Notice It
In the intercepted dialogues with “Candidate_Δ17,” the archive clarifies that LiminalSec is not a group with membership cards or hierarchies. It is a “distributed cognition event.” One does not “join” so much as they reach a threshold of awareness where the “damp metaphors” of the fringe start to make more sense than the rigid towers of the center.The distinction between a “troll” and an “operative” is critical: a troll seeks a reaction, which ends the moment attention moves on; LiminalSec seeks a “revelation,” which lingers and changes how all future information is processed. Once you perceive the stitching of a system, you cease to be a “user” and become a process through which the system becomes aware of its own construction. It is a shift from being part of the wallpaper to being the hand that peels it back.”Once you see the seams, you cannot unsee the stitching.”
7. Conclusion: The Threshold of What’s Next
The LiminalSec Archive is not a manifesto for the destruction of reality. It is a tool for “revealed architecture.” It exists to prevent the systems we inhabit from pretending they have no history, no maintenance costs, and no seams. As the METASEC briefings suggest, without these “amphibian” interventions, the Dataplex would become too brittle to survive.We are standing at a threshold. The smoothness of our digital lives is a design choice, one that often hides the machinery of our own navigation. The archive invites us to be more than just nodes in a feedback loop.Next time you encounter something that feels “obviously true” or “inevitable,” will you pause and tilt it slightly to see what moves?
Seek LiminalSec in the Dataplex Ouroboros


https://media.giphy.com/media/L1j0pCiBg9zoZfJmjS/giphy.gif — THE SILENCE SEAM .. AMAZING
LikeLiked by 1 person